At the heart of countless cyberattacks is a single flaw in the code making up a piece of software. Carnegie Mellon University CyLab researchers are focusing their efforts on improving software security in a variety of ways, from creating automated methods of finding and fixing software bugs to verifying the security of software without compromising its performance.
People
Learn who at CyLab is working in software security.
Subtopics
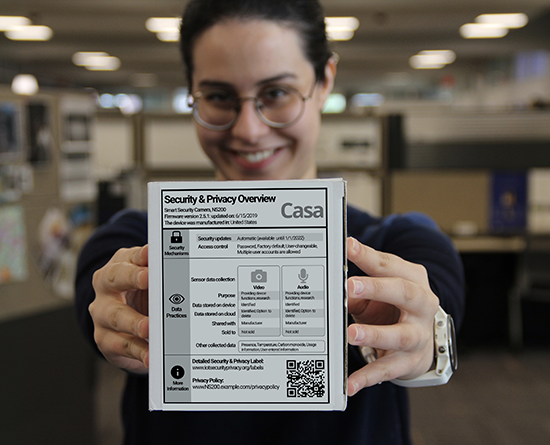
We have researchers working in the following subtopics of applications of security and privacy. Check out each of their research:
Explore Other Research Topics